Email and calendar
made better
Fast, private email hosting for you or your business.



“I have used Fastmail for years and never had one problem. Not one.”
“I migrated from Google Workspace to Fastmail and would never go back.”
“I've been using Fastmail for more than ten years. I couldn't be happier.”
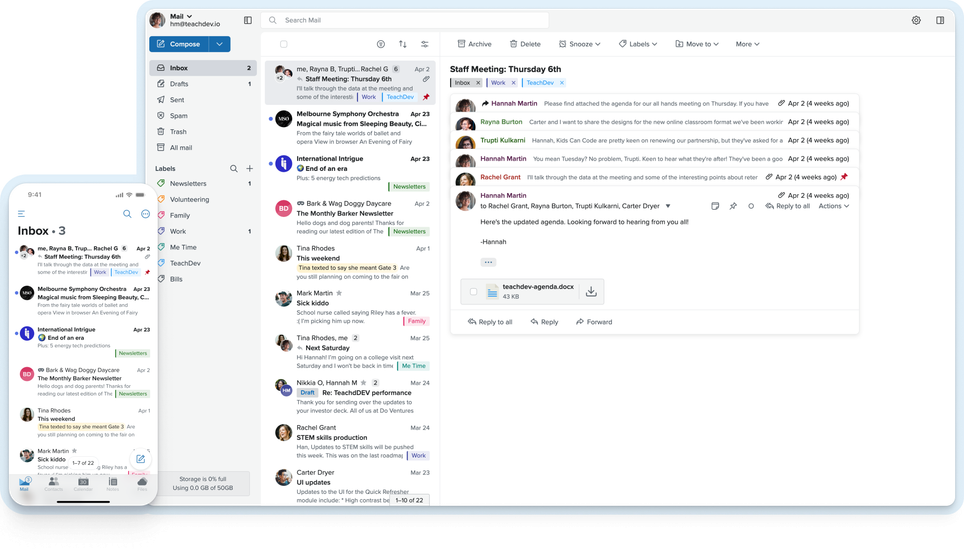
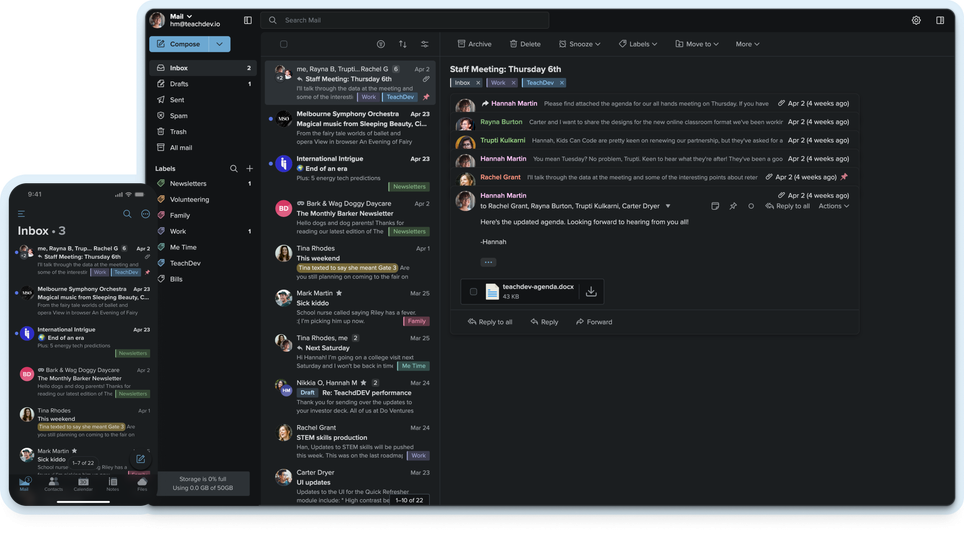
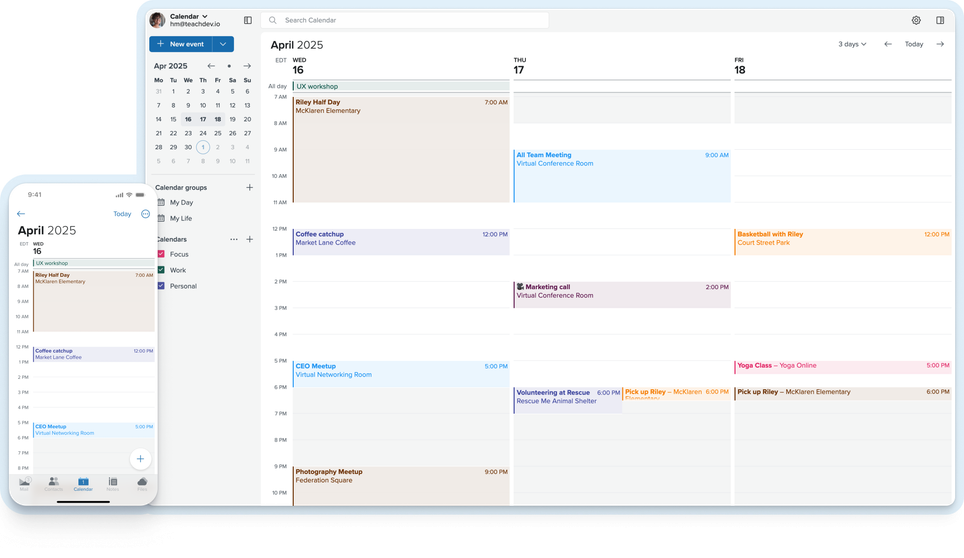
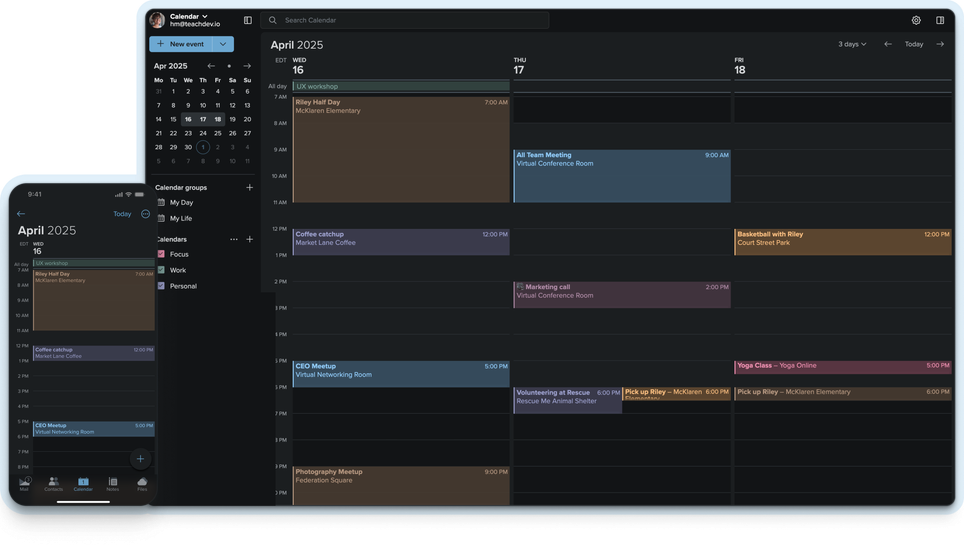
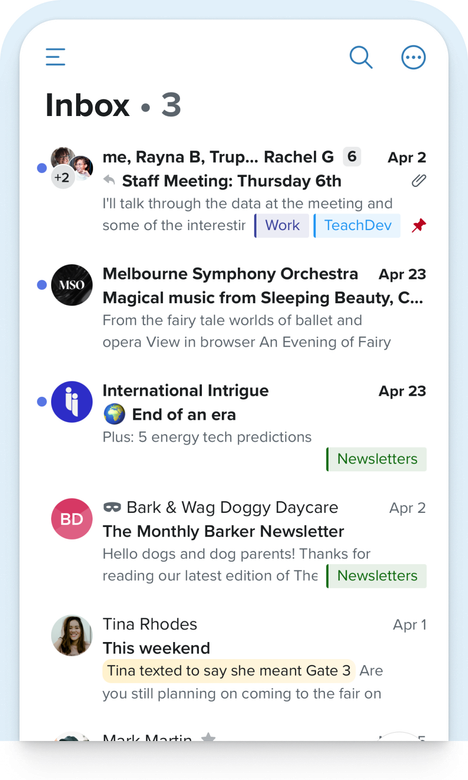
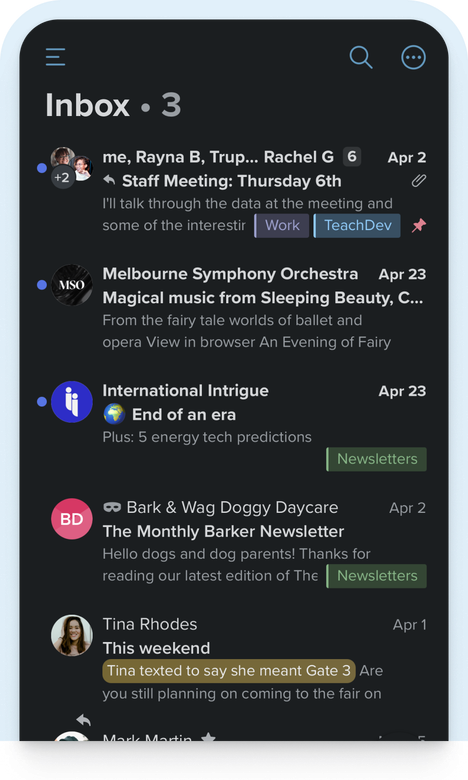
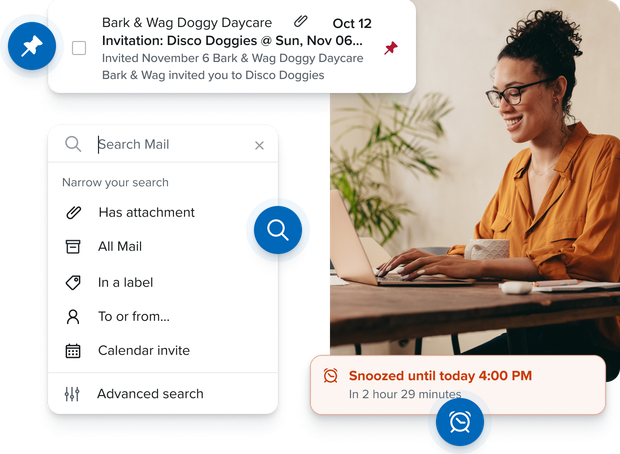
Better for staying on top of it all
See how much better email and calendars can be when it’s super fast, has great search, and surfaces the information you need, right when you need it.
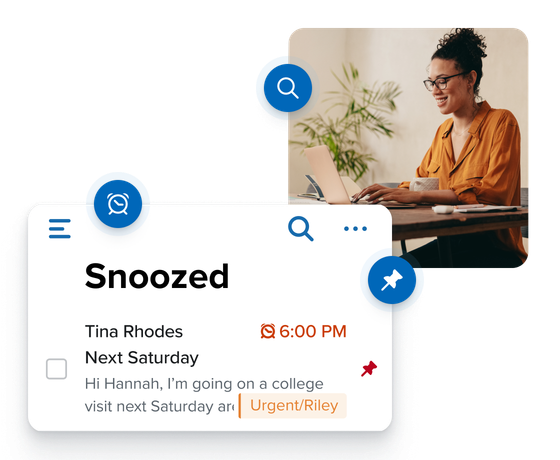
Boost your productivity
- Pin important messages to the top of your inbox for instant access.
- Snooze tickets and bills to just when you need them.
- Find any message in seconds with our powerful search.
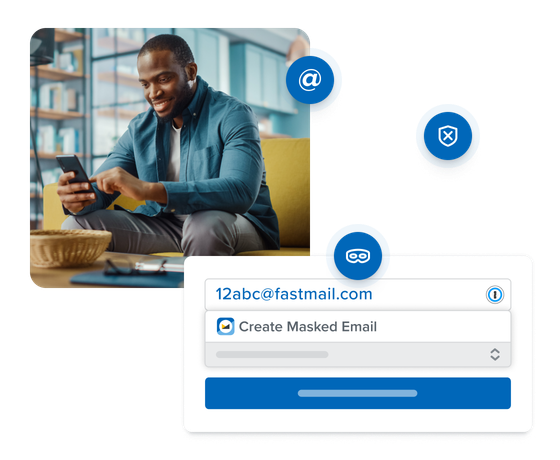
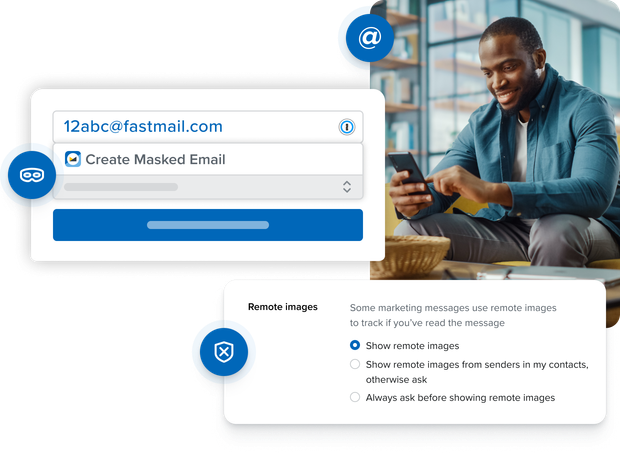
Protect your privacy
- Keep your real email address private with Masked Email.
- Use aliases to keep your side hustles separate.
- Stop spy pixels tracking your location.
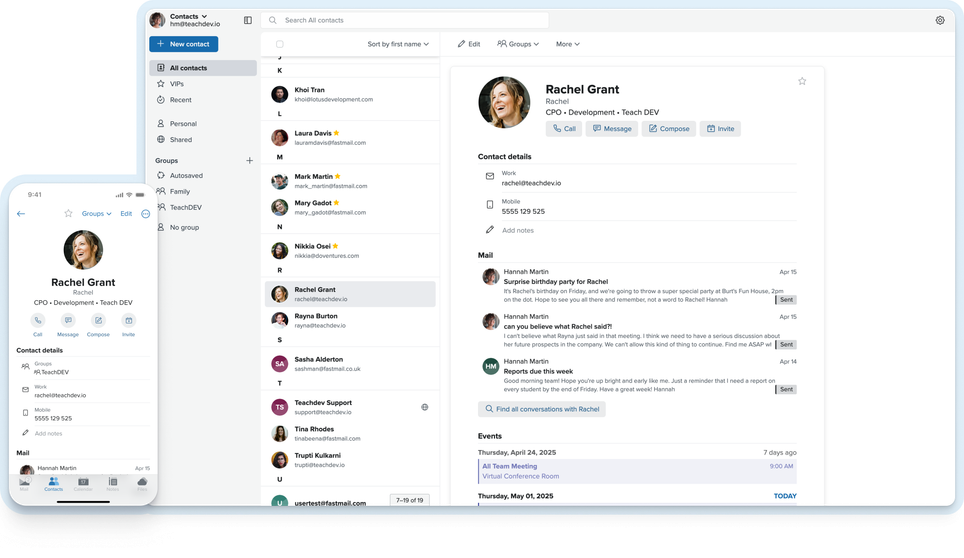
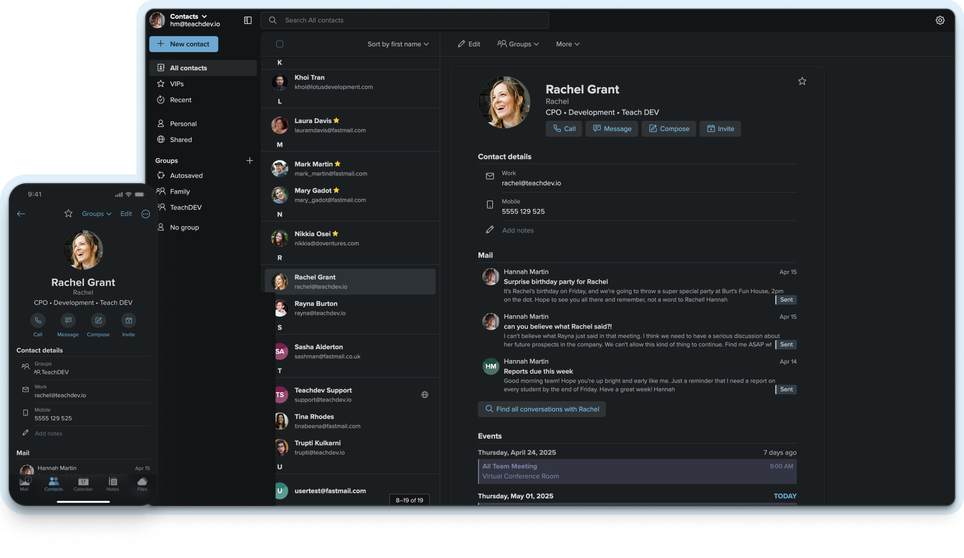
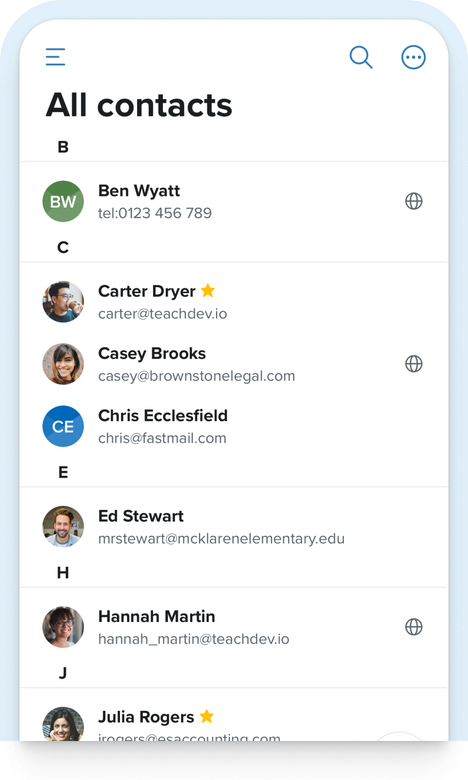
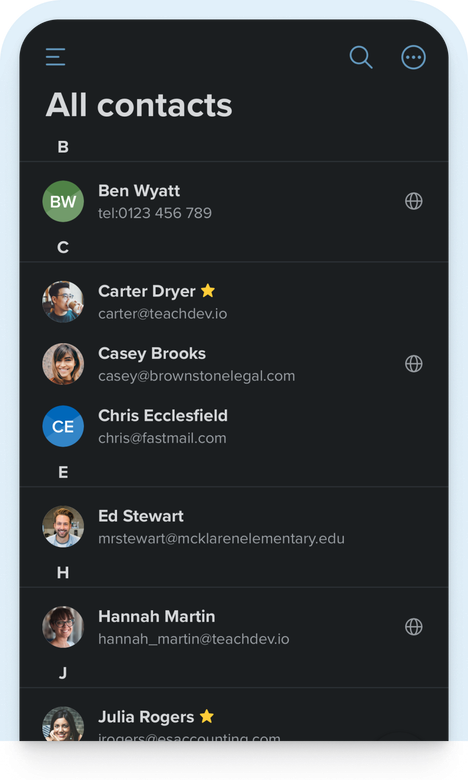
Get organized
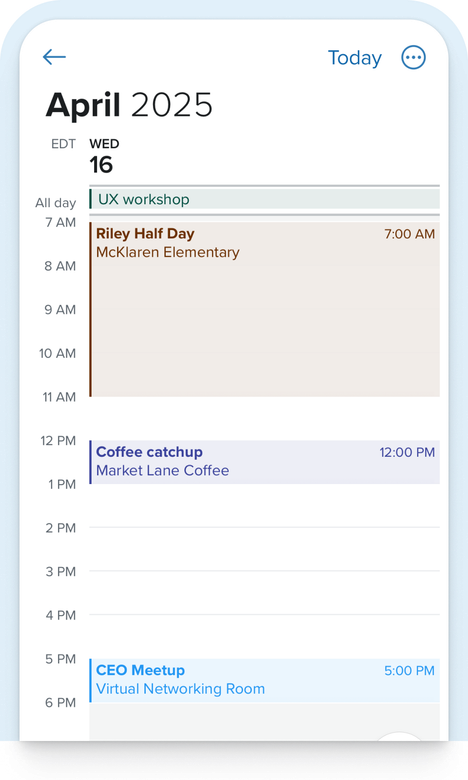
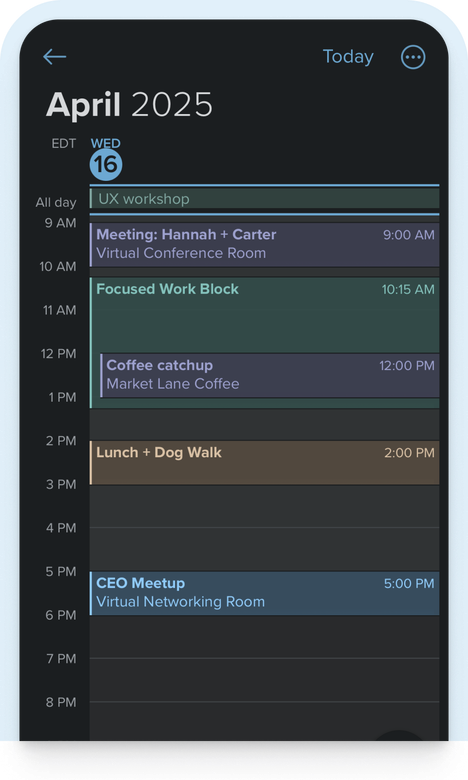
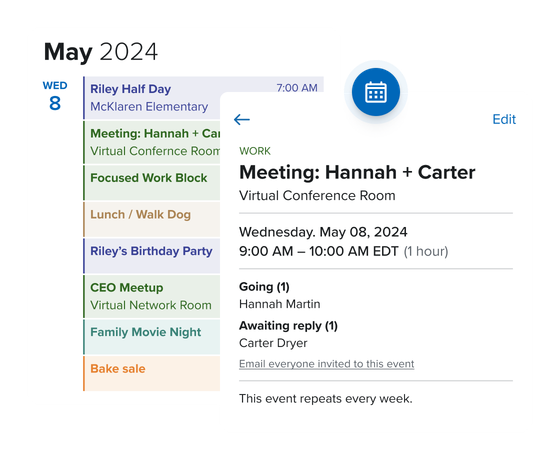
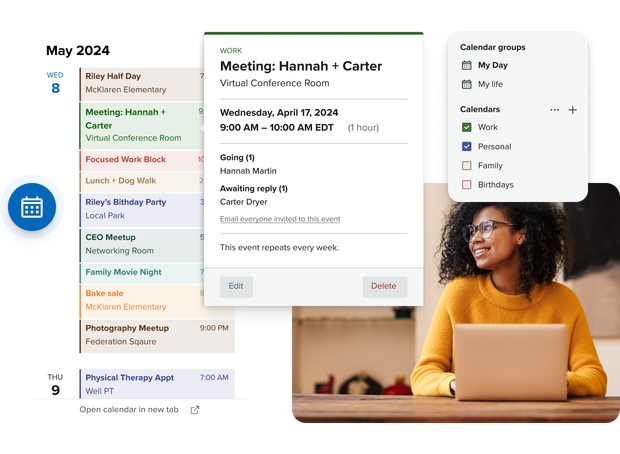
- Stay on schedule with our fast, beautiful calendar.
- Know exactly what’s changed when someone updates an event.
- See all your events in one place by adding your Google or iCloud calendars.
Stay focused
- Avoid unwanted interruptions with VIP-only notifications.
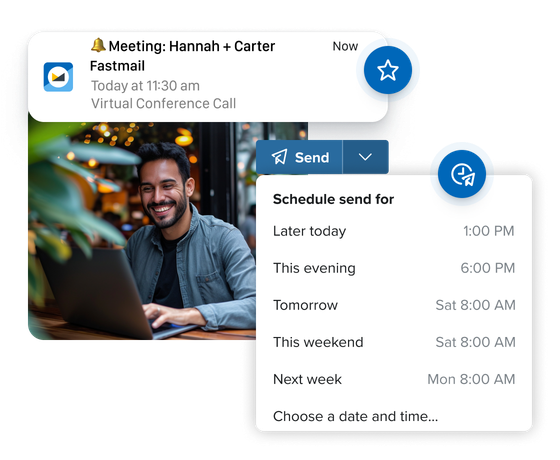
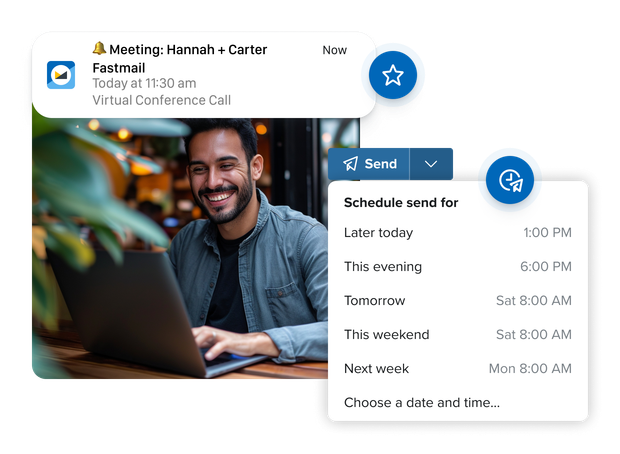
- Work on your time with scheduled send.
Better isn’t easy to describe, but you know it when you see it
Best alternative to Gmail and iCloud for email, calendars, and contacts!
Jon Henshaw
Founder of Coywolf
I have used Fastmail for years and found them consistently excellent.
Dylan Beattie
Creator of the Rockstar programming language

Fastmail rocks! It’s secure, private, independent, and has a Gmail transfer tool. You won’t regret the move.
Vicky Brasseur
Open source expert and author

Better for your peace of mind
Private
Free email isn’t really free: you’re paying with your privacy. As a paid service, we only serve you, our customer. This means we have no split loyalties, no mining of your personal data, no sharing it with third parties, and no ads, ever.
See plans
Secure
Your email unlocks access to everything you do on the web. It’s the history of where you’ve been, what you buy, and who you know. We take great measures to keep it secure, backed up, and always available to you — and no one else.
Learn about email security
Personal support
From “how do I get started” to “I’ve lost my phone” panic, when you need that extra helping hand, we’re here for you. Our support team are online 24/7, providing personal support to ensure your email runs smoothly.
Get support
No lock-in
We’ve been delivering a better service for over 20 years, growing all that time — because once you’ve tried it, you won’t settle for anything else. People stay because we’re the best, not because it’s too hard to get your data out. After all, it’s your data, not ours.
Read our values
Better for everyone
We won’t let email become just another closed messaging service owned by big tech.
We don’t just make a better email service. We also make email better for everyone with our work advancing open standards and leading industry co-operation. We employ the top experts on email and calendaring, working on everything from email authentication to calendar interoperability.
Our contributions include the development of JMAP, the next-generation open sync protocol, and a wide range of open-source code used by organizations around the world. Our work keeps the internet open, and stops email becoming just another walled garden.
Read about open source and standards
Featured in:
Take control of your inbox
Easily migrate your mail, calendars, and contacts.