Lock up your passwords
Post categories

Alum
We’ve previously mentioned the importance of having a secure password for your FastMail account. Let’s have a closer look at keeping your passwords safe online.
Passwords are everywhere. From something as relatively trivial as your shopping loyalty cards, through online shopping services, up to highly sensitive accounts with your bank, domain registration or email account.
Passwords get reused. There are so many places which require passwords and much as we’d like to have one highly secure password per site (even with the help of a password manager), the reality is that we all use the same password in more than one place.
Why is this bad? If one website is hacked and a database of passwords and matching email usernames is obtained by an attacker, then it’s likely that the same username and password combination will work on other websites.
If your Pokemon Go account username and password is discovered, you might shed a tear for all those Pokemon you’ve collected. But you might not realise that an attacker will continue to try your username and password against other commonly used websites such as eBay, PayPal, banks, and email services.
Email passwords are critical (mostly). You will have at least one email account that forms your online identity. It is a gateway to every other service. If an attacker has access to your email account: they can request password resets on websites as if they were you. This lets the attacker hijack your other accounts and locks you out.
We say ‘mostly’, because not all email accounts are equal. You may have a disposable email account registered to let you post funny cat pictures on the internet. If this is compromised, no problem. Our focus on email password security is for the email accounts that hold information you care about, or are tied to sites you rely on.
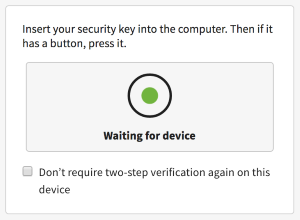
Help me, FastMail: you’re my only hope. If you can’t reuse a password but there’s too many passwords to remember them all, what’s to be done? Two-step verification to the rescue! Two-step verification (also known as two-factor authentication or 2FA) protects your password because your password alone can’t be used to log in: you need a second piece of information which is usually something physical you carry with you. This can be either a security key that plugs into your computer, or a code generated by an app on your phone.
Even if an attacker guesses your password, or obtains it from another site, they still can’t log in to an account protected by two-step verification because they don’t have the second piece of information!
[
FastMail’s security system. We want you to keep your account safe. But we also want to make it easy for you to protect your account.
- Protect your web login and FastMail app login.
- Our new two-step verification support is simple to set up and easy to use. You can use an app on your phone, a security device, or even SMS. You can configure multiple options in case you need to log in but don’t have your security device with you.
- Once you’ve verified your login from a particular device, you can opt to not require two-step verification again on that device. Makes life simple for you, but still foils an attacker trying to log in from another computer. Good to use if you’re not accessing your account at a public location like an internet cafe.
- Protect your logins from other programs and apps.
- Programs like mail clients on a desktop computer, or calendaring apps on your phone can’t use two-step verification to log in. Protect your account by creating an app-specific password for each program needing access to your data at FastMail.
- If you lose a device you can revoke access to just one app rather than having to change your password everywhere.
- A FastMail app-specific password can be locked down to ensure the login can only access the data it needs.
- Proactive management
- You can revoke an app password at any time if the device it belongs to is lost or compromised.
- You can see all the places you are currently logged into your account, and remotely log out anything suspicious or you don’t need (perhaps you accidentally left yourself logged in at a friend’s house).
- You can revoke a computer’s “trusted” status at any time, forcing the next login to require two-step verification.
I don’t think I need two-step verification. You might think you don’t need to bother with 2FA if you only ever access your email from a desktop client like Mail on Mac OSX or Outlook on Windows. Just remember: attackers will be using the web login to try to gain access to your account. You still want to lock up your password with 2FA. (It’s no use locking up the side door to your house if your front door is left unlocked!)
Interested in a brief history of passwords? Our lovely Rob N gave a talk this year at CompCon Australia 2016, covering such topics as: “Passwords are terrible”, and “Passwords have always been terrible”; “Keeping passwords secret” and finally “Making passwords useless”.
Got any security questions or recommendations? Tweet us @FastMail using the hashtag #securitymatters.
